[metaslider id=2951] … Read More
Optimizing the Security Awareness of your End-Users
End-users can be the weakest link in your infosec defense. But according to KnowBe4 founder and CEO Stu Sjouwerman, there is something you can do about that – if you implement the right behavioral diagnostics and focus your training needs on individual users’ actual weaknesses.
According to ISACA - Cyber Threats Up but no increase in Ransomware
Ransomware attacks are significantly declining despite an increase in cyberattacks generally, according to the global IT association ISACA.
Written by Peter Dinham - ITWire
In its State of Cybersecurity 2018 research study just released, ISACA reveals that last year, 62% of respondents experienced a ransomware attack, compared to 45% this year — a 17-point drop.
According to ISACA, the drop in ransomware attacks is likely because organisations are significantly better prepared after last year’s WannaCry and NotPetya attacks, with 82% of respondents saying that their enterprises now have ransomware strategies in place. In addition, 78% said they have a formal process in place— up 25-points from last year.
“While these findings are positive, the data show that ransomware attacks may have been displaced by cryptocurrency mining, which is becoming more frequent,” said ISACA.
“Cryptocurrency mining malware can operate without direct access to the file system, making them harder to detect—and as the prices of cryptocurrencies increase, the economics of cryptocurrency mining malware becomes better for the attacker.
“Additionally, the three most common attack vectors remain unchanged from last year - phishing, malware and social engineering.”
The research also shows that 50% of the 2,366 security leaders surveyed have seen an increase in cyberattack volumes relative to last year and, in addition, 80% of respondents said they are likely, or very likely, to be attacked this year — a statistic that ISACA says remains unchanged from last year’s study.
According to ISACA, active defence strategies are highly effective, but underutilised.
The research also found that nearly 4 out of 10 respondents (39%) are not at all familiar or only slightly familiar with active defence strategies (e.g., honeypots and sinkholes), and of those who are familiar with active defence strategies, just over half are actually using them.
“This is a missed opportunity for security leaders and their organisations,” said Frank Downs, director of cybersecurity at ISACA.
“ISACA’s research indicates that active defence strategies are one of the most effective countermeasures to cyberattacks. A full 87% of those who use them indicate that they were successful.”
The ISACA report suggests enterprises must be better prepared with focused attention on several areas, and makes several recommendations, including:
- Investing in talent—With attacks still on the rise, enterprises must continue to invest in finding, retaining and training skilled cyber security professionals
- Exploring further automation benefits—Enterprises should consider automation-driven strategies and tools for detection and to support recovery and response efforts
- Ensuring appropriate investment in security controls—With attack vectors (phishing, malware and social engineering) minimally changing, existing control types are still valid and useful. Enterprise investment and attention to security controls should increase in line with the frequency of these attack vectors.
Phishing Attack Bypasses Two-Factor Authentication
Hacker Kevin Mitnick demonstrates a phishing attack designed to abuse multi-factor authentication and take over targets’ accounts.
Businesses and consumers around the world are encouraged to adopt two-factor authentication as a means of strengthening login security. But 2FA isn’t ironclad: attackers are finding ways to circumvent the common best practice. In this case, they use social engineering.
A new exploit, demonstrated by KnowBe4 chief hacking officer Kevin Mitnick, lets threat actors access target accounts with a phishing attack. The tool to do this was originally developed by white hat hacker Kuba Gretzky, who dubbed it evilginx and explains it in a technical blog post.
It starts with typosquatting, a practice in which hackers create malicious URLs designed to look similar to websites people know. Mitnick starts his demo by opening a fake email from LinkedIn and points out its origin is “llnked.com” - a misspelling people will likely overlook.
Those who fall for the trick and click the email’s malicious link are redirected to a login page where they enter their username, password, and eventually an authentication code sent to their mobile device. Meanwhile, the attacker can see a separate window where the victim’s username, password, and a different six-digit code are displayed.
“This is not the actual 6-digit code that was intercepted, because you can’t use the 6-digit code again,” Mitnick says in the demo. “What we were able to do was intercept the session cookie.”
With the session cookie, an attacker doesn’t need a username, password, or second-factor code to access your account. They can simply enter the session key into the browser and act as you. All they have to do is paste the stolen session cookie into Developer Tools and hit Refresh.
It’s not the first time 2FA has been hacked, says Stu Sjouwerman, founder and CEO at KnowBe4. “There are at least ten different ways to bypass two-factor authentication,” he explains in an interview with Dark Reading. “They’ve been known about but they aren’t necessarily well-published … most of them are flying under the radar.”
These types of exploits are usually presented as concepts at conferences like Black Hat. Mitnick’s demo puts code into context so people can see how it works. This can be used for any website but an attacker will need to tweak the code depending on how they want to use it.
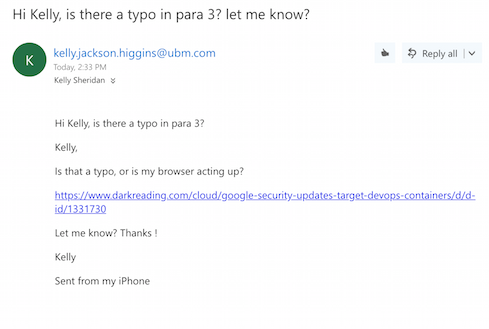
To show how the exploit can make any site malicious, Sjouwerman sent me an email tailored to look like it came from Kelly Jackson Higgins, reporting a typo in an article of mine:
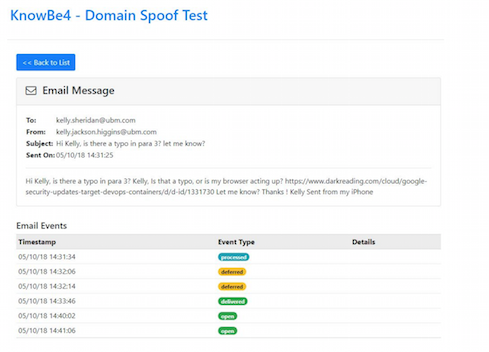
When I clicked the link, I ultimately ended up on Dark Reading but was first redirected to a site owned by the “attacker” (Sjouwerman). In a real attack scenario, I could have ended up on a truly malicious webpage where the hacker could launch several different attacks and attempt to take over my machine. Sjouwerman sent a screenshot of what he saw while this happened:
Event types go from processed, to deferred, to delivered, to opened.
“You need to be a fairly well-versed hacker to do this - to get it set up and have the code actually working,” he notes. This is a one-on-one attack and can’t be scaled to hit a large group of people at the same time. However, once the code works, the attack is fairly simply to pull off.
“You need to have user education and training, that’s a no-brainer, but you also have to conduct simulated phishing attacks,” Mitnick says in his demo.
Sjouwerman emphasizes the importance of putting employees through “new school” security awareness training, as opposed to the “death by PowerPoint” that many employees associate with this type of education. Instead of putting them through presentations, he recommends sending them phishing attacks and conducting online training in the browser.
The four myths hampering cybersecurity maturity
We’ve seen tremendous advances in technology over the last 15 years or so, but security continues to struggle as much today as it did a decade ago.
A large part of the problem is that security professionals and their leaders have bought into myths that hamper their ability to move their organizations forward and achieve maturity – the kind of maturity that’s necessary to be able to survive and recover from a cyber attack.
In no particular order, here are the four myths that security organizations need to stop believing and how they should move forward.
Myth #1: Cybersecurity risk can be eliminated
As a security professional, you know this isn’t true, right? Cybersecurity risk cannot be eliminated. It can only be managed. However, judging by the enormous sums of money companies waste attempting to achieve impenetrability, it seems this myth has life in it yet.
The problem is at the top: Senior executives and Board of Directors don’t understand the nature of cyber security. They think if they throw enough money at the problem, it will go away. But we know that’s not the case. Senior executives and Board of Directors must be educated on the inevitable nature of a cyberattack and how that risk is managed.
Myth #2: There’s a cybersecurity silver bullet somewhere-we just haven’t found it yet
Nothing will prevent your organization from being the target of a cyberattack. There isn’t a single technology solution, employee training/awareness program, insurance policy, contractual agreement, or anything else that can protect your organization 100% from a cyberattack.
The best you can do is implement a balanced, yet strategic risk management program that enables the CEO to stand in front of the executive suite and explain with confidence, “We understand our risk exposure, and we have the ability and financial resources to recover from an event should the inevitable happen.”
Myth #3: The security organization effectively operates as a silo
How much success has your security organization had to date? If it’s operating in a silo, that success is limited. Yes, the security person is primarily responsible for cyber security, but he/she can’t do it alone. To be effective, security must be a team sport. This team includes the employees who handle employee training and awareness, people who oversee business continuity and operations, staff who purchase cyber insurance, the lawyers who contract with clients and suppliers and, of course, the C-suite and Board of Directors. These groups need to work together to the same end, otherwise there will always be gaps in your security posture.
Myth #4: Regulatory compliance = security
It amazes me that organizations continue to use regulatory compliance requirements as the primary framework for their cybersecurity efforts. While newer regulations and frameworks like the NIST Cyber Security Framework and New York Department of Financial Services guidelines are risk-based, the vast majority of organizations I speak to aren’t using them appropriately. Organizations need a maturity-based cyber risk management framework with short-, medium-, and long-term benchmarks. The framework should be reviewed and updated quarterly and tested annually.
It can be difficult to explain to the Board the inevitability of a cyber attack, or to align disparate groups to work toward the same objective. But these things must be done if organizations are going to actually improve their security posture and mature their security programs. It’s time security professionals are honest with themselves-and with upper-management-and start making real progress toward resiliency.
KnowBe4 Attains SOC 2 Type I Compliance For The Hosted Phishing And Training Product Offerings
KnowBe4, Inc, the world’s largest security awareness training and simulated phishing platform, this week announced it has  successfully completed a Service Organization Controls (SOC) 2 Type I examination for the hosted phishing and training product lines, which help organizations address the human sources of risk associated with phishing attacks.
successfully completed a Service Organization Controls (SOC) 2 Type I examination for the hosted phishing and training product lines, which help organizations address the human sources of risk associated with phishing attacks.
With System and Organization Control audits (SOC) becoming more and more necessary to retain and engage new customers, many service companies are unsure whether a SOC 1 or SOC 2 audit will be suitable. Even though these audit exercises are largely the same from a procedural standpoint, they serve very different purposes for the customers. In this respect, companies ought to understand the differences between soc1 vs soc2. Created for entities operating in the rapidly expanding technology and cloud computing sector, SOC 2 compliance is an industry-standard in data security compliance. In pursuit of this industry-leading certification, organizations undergo a rigorous analysis that can include the following trust services criteria: security, availability, processing integrity, confidentiality, and privacy.
“Achieving this certification demonstrates our continued commitment and investment in larger compliance efforts to exceed enterprise standards and expectations with respect to data security,” said Stu Sjouwerman, Founder and CEO of KnowBe4.
360Avanced, Inc., an independent and qualified security Assessor in St Peterburg, FL, conducted the audit of KnowBe4’s platform, testing the suitability of design of controls, with a focus on security, availability and confidentiality principles in line with strict criteria.
The purpose of SOC standards are to help provide confidence and peace of mind for organizations and their third-party partners. KnowBe4 earned the SOC 2 certification because it has sufficient policies and strategies that are designed to satisfactorily protect their customers’ data.
For more information about KnowBe4’s security practice, visit: https://www.knowbe4.com/security