Oh boy. Uber is known for pushing the limits of the law and has dozens of lawsuits pending against it, but this one went too far and now comes the reckoning.
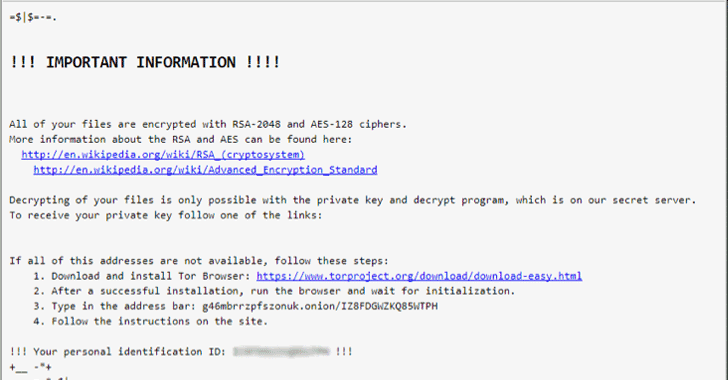
Bloomberg was first to report that hackers stole the personal data of 57 million customers and drivers from Uber, a massive breach that the company concealed for more than a year. Finally, this week, they fired their chief security officer and one of his deputies for their roles in keeping the hack under wraps, which included a $100,000 payment to the attackers to “delete the data”. Yeah, sure!
Victim Of A Simple Credentials Phishing Attack?
Here’s how the press describes the hack: Two attackers accessed a private GitHub coding site used by Uber software engineers and then used login credentials they obtained there to access data stored on an Amazon Web Services account that handled computing tasks for the company.
From there, the hackers discovered an archive of rider and driver information. Later, they emailed Uber asking for money, according to the company. If you read between the lines, that could very well be a simple credentials spear phishing scheme, done with some crafty social engineering, or perhaps careless developers leaving internal login passwords lying around online: