[metaslider id=2951] … Read More
Phishing Attack Bypasses Two-Factor Authentication
Hacker Kevin Mitnick demonstrates a phishing attack designed to abuse multi-factor authentication and take over targets’ accounts.
Businesses and consumers around the world are encouraged to adopt two-factor authentication as a means of strengthening login security. But 2FA isn’t ironclad: attackers are finding ways to circumvent the common best practice. In this case, they use social engineering.
A new exploit, demonstrated by KnowBe4 chief hacking officer Kevin Mitnick, lets threat actors access target accounts with a phishing attack. The tool to do this was originally developed by white hat hacker Kuba Gretzky, who dubbed it evilginx and explains it in a technical blog post.
It starts with typosquatting, a practice in which hackers create malicious URLs designed to look similar to websites people know. Mitnick starts his demo by opening a fake email from LinkedIn and points out its origin is “llnked.com” - a misspelling people will likely overlook.
Those who fall for the trick and click the email’s malicious link are redirected to a login page where they enter their username, password, and eventually an authentication code sent to their mobile device. Meanwhile, the attacker can see a separate window where the victim’s username, password, and a different six-digit code are displayed.
“This is not the actual 6-digit code that was intercepted, because you can’t use the 6-digit code again,” Mitnick says in the demo. “What we were able to do was intercept the session cookie.”
With the session cookie, an attacker doesn’t need a username, password, or second-factor code to access your account. They can simply enter the session key into the browser and act as you. All they have to do is paste the stolen session cookie into Developer Tools and hit Refresh.
It’s not the first time 2FA has been hacked, says Stu Sjouwerman, founder and CEO at KnowBe4. “There are at least ten different ways to bypass two-factor authentication,” he explains in an interview with Dark Reading. “They’ve been known about but they aren’t necessarily well-published … most of them are flying under the radar.”
These types of exploits are usually presented as concepts at conferences like Black Hat. Mitnick’s demo puts code into context so people can see how it works. This can be used for any website but an attacker will need to tweak the code depending on how they want to use it.
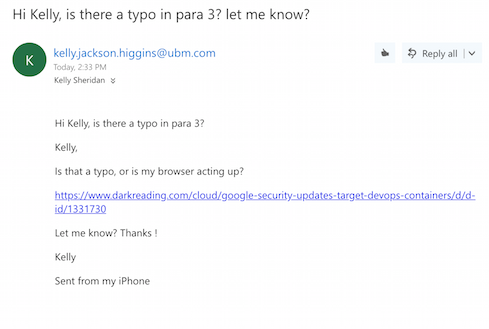
To show how the exploit can make any site malicious, Sjouwerman sent me an email tailored to look like it came from Kelly Jackson Higgins, reporting a typo in an article of mine:
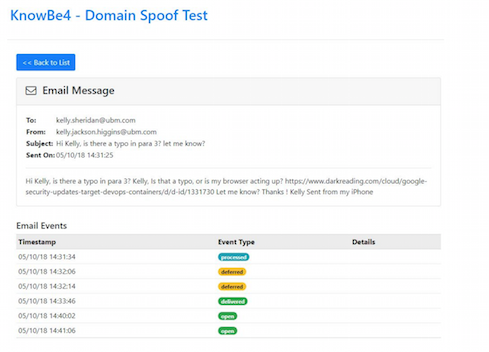
When I clicked the link, I ultimately ended up on Dark Reading but was first redirected to a site owned by the “attacker” (Sjouwerman). In a real attack scenario, I could have ended up on a truly malicious webpage where the hacker could launch several different attacks and attempt to take over my machine. Sjouwerman sent a screenshot of what he saw while this happened:
Event types go from processed, to deferred, to delivered, to opened.
“You need to be a fairly well-versed hacker to do this - to get it set up and have the code actually working,” he notes. This is a one-on-one attack and can’t be scaled to hit a large group of people at the same time. However, once the code works, the attack is fairly simply to pull off.
“You need to have user education and training, that’s a no-brainer, but you also have to conduct simulated phishing attacks,” Mitnick says in his demo.
Sjouwerman emphasizes the importance of putting employees through “new school” security awareness training, as opposed to the “death by PowerPoint” that many employees associate with this type of education. Instead of putting them through presentations, he recommends sending them phishing attacks and conducting online training in the browser.
Almost One Quarter Of Canadians Have Clicked On A Phishing Link
TORONTO, March 1, 2018 /CNW/ - Online payment fraud like phishing is a growing trend, and Canadians are worried about it. According to a new survey conducted by Interac Corp., Canadians are more likely to worry about payment fraud scams like phishing and skimming than home break-ins, vehicle theft and plane crashes.
And, almost one quarter of Canadians say they have clicked on a link that resulted in a phishing scam, while 64 per cent say they have been tempted to click on a link they weren’t completely sure was safe.
“As payment fraud increasingly migrates online through scams like phishing, the continued work we do with our partners to detect and prevent fraudulent activity has never been more important,” said Rob Fodor, Chief Data Scientist and VP of Fraud, Interac Corp. “It’s also why we feel strongly about arming Canadians with the information they need to spot, avoid and report any phishing scams they may come across.”
New-school security awareness training is a must to keep employees on their toes with security top of mind. Find out what percentage of your employees are phish-prone.
Organizations Are Failing To Learn From Phishing And Ransomware Attacks
By Stu Sjouwerman - February 28th, 2018
Warwick Ashford, security editor at ComputerWeekly had an interesting observation after reading CyberArk’s latest cyber threat report:
“Organisations are failing to learn from cyber attacks, and lax security practices are leaving organisations worldwide open to damaging cyber attacks”
“Respondents said the greatest cyber security threats they currently face are targeted phishing attacks (56%),insider threats (51%), ransomware or other malware (48%), unsecured privileged accounts (42%), and unsecured data stored in the cloud (41%).
There is a worrying lack of action by businesses to improve security following an attack across the global technology industry, according to the latest cyber threat report by privileged account security firm CyberArk.
The report also highlights poor practices concerning cloud and endpoint security, and from security professionals themselves, putting sensitive data, infrastructure, assets and even employers at risk.
Every organization has something of value to a cyber attacker, and greater investments in cloud technologies and DevOps processes mean the attack surface is expanding exponentially, and attackers continue to target and exploit privileged accounts, credentials and secrets to accomplish their goals, the report said.
Nearly half (46%) of IT security professionals rarely change their security strategy substantially, even after experiencing a cyber attack, according to a CyberArk-commissioned poll of 1,300 IT security decision makers, developers and line of business owners in seven countries.
This level of cyber security inertia and failure to learn from past incidents puts sensitive data, infrastructure and assets at risk, the CyberArk report said.
The survey also revealed that while 89% of IT security professionals believe securing an environment starts with protecting privileged accounts and more than four in 10 cite it as a top security risk, more than a quarter (28%) are not putting this knowledge into action.
Demands for flexibility
The proportion of users who have local administrative privileges on their endpoint devices increased from 62% in 2016 to 87% in 2018, a 25% increase the report said could indicate that employee demands for flexibility have been allowed to trump security best practices.
The survey findings suggest security inertia has infiltrated many organisations, with an inability to repel or contain cyber threats and the resultant impact on the business.
This inertia is reflected in the fact that 46% of respondents said their organisation cannot prevent attackers from breaking into internal networks every time it is attempted, 36% said that administrative credentials are stored in Word or Excel documents on company PCs, and half admitted their customers’ privacy or PII (personally identifiable information) could be at risk because their data is not secured beyond the legally-required basics.
The report notes that the automated processes inherent in cloud and DevOps mean that privileged accounts, credentials and secrets are being created at a prolific rate. If compromised, the report said these can give attackers a crucial jumping-off point to achieve lateral access to sensitive data across networks, data and applications or to use cloud infrastructure for illicit crypto mining activities.
The survey shows that while organisations increasingly recognise this security risk, they still have a relaxed approach towards cloud security, with half of organisations polled having no privileged account security strategy for the cloud and more than two-thirds (68%) relying on built-in security capabilities.
“There are still gaps in the understanding of who is responsible for security in the cloud, even though the public cloud suppliers are very clear that the enterprise is responsible for securing cloud workloads. Additionally, few understand the full impact of the unsecured secrets that proliferate in dynamic cloud environments and automated processes,” the report said.
Overcoming cyber security inertia, the report said, requires cyber security to become central to organisational strategy and behavior, not something that is dictated by competing commercial needs.
According to the survey, 86% of IT security professionals feel security should be a regular board-level discussion topic, and 44% said they recognize or reward employees who help prevent an IT security breach, increasing to nearly three quarters (74%) in the US.
However, only 8% of companies continuously perform red team exercises to uncover critical vulnerabilities and identify effective responses. Investing in regular red team exercises could help determine where to focus efforts and prioritize risk reduction, the report said.
Rich Turner, European vice-pesident at CyberArk, said cyber attackers are often able to penetrate traditional perimeter defences when targeting organisations that have not moved with the times. This was cross-posted with grateful acknowledgements.
Report: 52% of companies sacrifice security to expedite projects
Organizations can be exposed to vulnerabilities when professionals prioritize a deadline over security, according to research from Threat Stack.
- 52% of companies admit to cutting corners on security to meet a project deadline. — Threat Stack, 2018
- 68% of executives said their CEO doesn’t want the security or DevOps teams to do anything that could slow a project down. — Threat Stack, 2018
More than half of companies admit to loosening security measures to expedite projects or meet deadlines, a new Threat Stack report found.
In a survey of over 200 executives, 52% said their company had prioritized a deadline or objective over the firm’s security. The emphasis on speed over security could leave holes in a project, leaving a company vulnerable.
The focus on speed comes from pushback on both sides of a project, the report found. Over two-thirds—68%—of respondents said their CEO asks the DevOps and security teams to not do anything that would slow a project, while 62% said their operations team sometimes fights new security efforts.
The majority of respondents said SecOps is important for their organization, but only 35% said it was a complete or mostly complete project at their company. At 18% of companies, SecOps isn’t established at all, the report found.
“The vast majority of companies are bought-in, but, unfortunately, a major gap exists between intent of practicing SecOps and the reality of their fast-growing businesses. It’s important that stakeholders across every enterprise prioritize the alignment of DevOps and security,” Brian Ahern, Threat Stack CEO, said in the press release.
Most of the challenges come from organizational alignment, the report found, as DevOps and security teams might be operating in different silos.
The discrepancy suggests companies should agree and focus on security to ensure their company remains safe, even under pressure from a deadline or the competition. More at: https://www.techrepublic.com/article/report-52-of-companies-sacrifice-security-to-expedite-projects/#ftag=RSS56d97e7
The four myths hampering cybersecurity maturity
We’ve seen tremendous advances in technology over the last 15 years or so, but security continues to struggle as much today as it did a decade ago.
A large part of the problem is that security professionals and their leaders have bought into myths that hamper their ability to move their organizations forward and achieve maturity – the kind of maturity that’s necessary to be able to survive and recover from a cyber attack.
In no particular order, here are the four myths that security organizations need to stop believing and how they should move forward.
Myth #1: Cybersecurity risk can be eliminated
As a security professional, you know this isn’t true, right? Cybersecurity risk cannot be eliminated. It can only be managed. However, judging by the enormous sums of money companies waste attempting to achieve impenetrability, it seems this myth has life in it yet.
The problem is at the top: Senior executives and Board of Directors don’t understand the nature of cyber security. They think if they throw enough money at the problem, it will go away. But we know that’s not the case. Senior executives and Board of Directors must be educated on the inevitable nature of a cyberattack and how that risk is managed.
Myth #2: There’s a cybersecurity silver bullet somewhere-we just haven’t found it yet
Nothing will prevent your organization from being the target of a cyberattack. There isn’t a single technology solution, employee training/awareness program, insurance policy, contractual agreement, or anything else that can protect your organization 100% from a cyberattack.
The best you can do is implement a balanced, yet strategic risk management program that enables the CEO to stand in front of the executive suite and explain with confidence, “We understand our risk exposure, and we have the ability and financial resources to recover from an event should the inevitable happen.”
Myth #3: The security organization effectively operates as a silo
How much success has your security organization had to date? If it’s operating in a silo, that success is limited. Yes, the security person is primarily responsible for cyber security, but he/she can’t do it alone. To be effective, security must be a team sport. This team includes the employees who handle employee training and awareness, people who oversee business continuity and operations, staff who purchase cyber insurance, the lawyers who contract with clients and suppliers and, of course, the C-suite and Board of Directors. These groups need to work together to the same end, otherwise there will always be gaps in your security posture.
Myth #4: Regulatory compliance = security
It amazes me that organizations continue to use regulatory compliance requirements as the primary framework for their cybersecurity efforts. While newer regulations and frameworks like the NIST Cyber Security Framework and New York Department of Financial Services guidelines are risk-based, the vast majority of organizations I speak to aren’t using them appropriately. Organizations need a maturity-based cyber risk management framework with short-, medium-, and long-term benchmarks. The framework should be reviewed and updated quarterly and tested annually.
It can be difficult to explain to the Board the inevitability of a cyber attack, or to align disparate groups to work toward the same objective. But these things must be done if organizations are going to actually improve their security posture and mature their security programs. It’s time security professionals are honest with themselves-and with upper-management-and start making real progress toward resiliency.
KnowBe4 Attains SOC 2 Type I Compliance For The Hosted Phishing And Training Product Offerings
KnowBe4, Inc, the world’s largest security awareness training and simulated phishing platform, this week announced it has  successfully completed a Service Organization Controls (SOC) 2 Type I examination for the hosted phishing and training product lines, which help organizations address the human sources of risk associated with phishing attacks.
successfully completed a Service Organization Controls (SOC) 2 Type I examination for the hosted phishing and training product lines, which help organizations address the human sources of risk associated with phishing attacks.
With System and Organization Control audits (SOC) becoming more and more necessary to retain and engage new customers, many service companies are unsure whether a SOC 1 or SOC 2 audit will be suitable. Even though these audit exercises are largely the same from a procedural standpoint, they serve very different purposes for the customers. In this respect, companies ought to understand the differences between soc1 vs soc2. Created for entities operating in the rapidly expanding technology and cloud computing sector, SOC 2 compliance is an industry-standard in data security compliance. In pursuit of this industry-leading certification, organizations undergo a rigorous analysis that can include the following trust services criteria: security, availability, processing integrity, confidentiality, and privacy.
“Achieving this certification demonstrates our continued commitment and investment in larger compliance efforts to exceed enterprise standards and expectations with respect to data security,” said Stu Sjouwerman, Founder and CEO of KnowBe4.
360Avanced, Inc., an independent and qualified security Assessor in St Peterburg, FL, conducted the audit of KnowBe4’s platform, testing the suitability of design of controls, with a focus on security, availability and confidentiality principles in line with strict criteria.
The purpose of SOC standards are to help provide confidence and peace of mind for organizations and their third-party partners. KnowBe4 earned the SOC 2 certification because it has sufficient policies and strategies that are designed to satisfactorily protect their customers’ data.
For more information about KnowBe4’s security practice, visit: https://www.knowbe4.com/security