[metaslider id=2951] … Read More
Archives for August 2017
SyncCrypt ransomware able to sneak past most antivirus defenses
From SC Magazine - August 17, 2017 - Doug Olenick,
A new ransomware called SyncCrypt is using a unique method of downloading the malicious files that makes it very hard for an antivirus program to detect.
SyncCrypt was detected by Emisoft researcher xXToffeeXx, reported Bleeping Computer, and is spread via spam emails containing an attachment with .wsf (Windows Script File) files. What is unusual about this, other than a .wsf file being used – which is rare – said Bleeping Computer founder Lawrence Abrams, is the .wsf will download an image with embedded .zip files containing the ransomware.
“This method has also made the images undetectable by almost all antivirus vendors on VirusTotal,” Abrams said.
Once the email is opened and the target decides to open the attachment, the social engineering plan being used has the document being listed as a court order, a JavaScript script activates that downloads the image. If the victim clicks on the downloaded image the cybercriminal’s sense of humor, or perhaps musical taste, appears when an image of Olafur Arnalds’ album titled “& They Have Escaped the Weight of Darkness” is shown.
However, whether or not the image is opened the .zip file is downloaded and its contents, a sync.exe, readme.html and readme.png, are extracted, Abrams said. The good news is that while image file tends to pass through most antivirus files contained inside the .zip file are more susceptible to detection. Although Bleeping Computer found that VirusTotal still detected them less than 50 percent of the time.
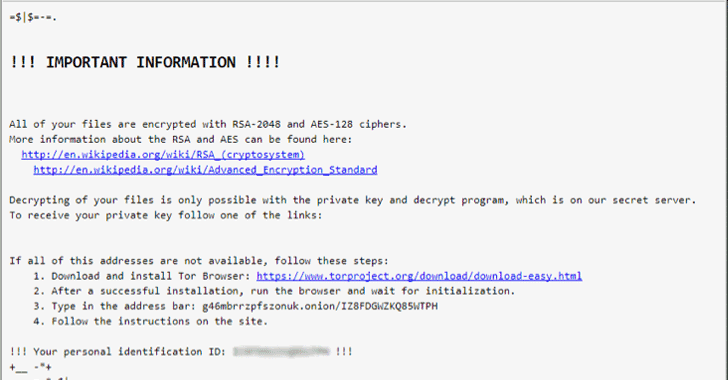
If properly installed the files are encrypted with a .kk extension and then the ransom note appears giving the victim 48 hours to pay about 0.1 bitcoin.
At this time there is no way to decrypt the files and the best defense is to ensure all files are properly backed up.
Two Dangerous Ransomware Are Back – Protect Your Computers
From the Hacker News - Swati Khandelwal
Ransomware has been around for a few years but has become an albatross around everyone’s neck—from big businesses and financial institutions to hospitals and individuals worldwide—with cyber criminals making millions of dollars.
In just past few months, we saw a scary strain of ransomware attacks including WannaCry, Petya and LeakerLocker, which made chaos worldwide by shutting down hospitals, vehicle manufacturing, telecommunications, banks and many businesses.
Before WannaCry and Petya, the infamous Mamba full-disk-encrypting ransomware and the Locky ransomware had made chaos across the world last year, and the bad news is—they are back with their new and more damaging variants than ever before.
Diablo6: New Variant of Locky Ransomware
First surfaced in early 2016, Locky has been one of the largest distributed ransomware infections, infecting organisations across the globe.
By tricking victims into clicking on a malicious attachment, Locky ransomware encrypts nearly all file formats on a victim’s computer and network and unlocks them until the ransom in Bitcoins is paid to attackers.
The ransomware has made many comebacks with its variants being distributed through Necurs botnet and Dridex botnet.