[metaslider id=2951] … Read More
The buzzword in 2015 was cyber threat intelligence (CTI) - everyone wanted useful data and analytical tools for next-gen cyber security to detect and respond to threats faster. The industry responded by providing a plethora of CTI products.
Matt Willems, a four-year, Labs Engineer, at LogRhythm has written a good overview of CTI and SIEM. Of course it is from a LogRhythm perspective.
He works closely with the Machine Data Intelligence team to collect consistent data for its Co-Pilot Program, develop new rule blocks for advanced correlation and builds parsing rules to support new devices. He also provides Incident Response support—analysing and interpreting data and delivering up-to-date content for the Knowledge Base to neutralize threats faster.
He starts by defining what cyber threat intelligence means and how to leverage successfully the information that is already in the SIEM ecosystem.
What is Cyber Threat Intelligence?
SC Magazine’s free Cyberthreat Intelligence e-book, (registration required) discusses CTI, the benefits of integrating into an organization’s defence strategy, as well as the different threat sharing initiatives and alliances.
Gartner defines CTI as evidence-based knowledge - including context, mechanisms, indicators, implications and actionable advice - about an existing or emerging menace or hazard to assets that can be used to inform decisions regarding the subject’s response to that menace or hazard.
“It can also be described as the process of detecting potential and actual threats using evidenced-based data, responding to them and defeating the attackers using forensic and logical data the attackers themselves leave behind,” according to SC Magazine’s Cyberthreat Intelligence e-book.
Without actionable data, there is no proactive defence. An effective CTI sets up the appropriate countermeasures automatically for drastically improved detection and response times.
Next-Gen Log Management to Facilitate CTI
CTI requires a log management tool [such as LogRhythm] to correlate the information to make the raw data collected actionable.
“The absolute minimum barrier to entry is a security information and event management (SIEM) or log management product of some sort. Then you at least have something to correlate the information that’s coming into your security ecosystem,” says Andrew Hay, CISO at DataGravity.
LogRhythm contextually structures every log message to store and understand what the data means.
Identify Nefarious Activity with a Distributed Set of Data
Every attack is different. All cyber-attacks have indicators of compromise (IOCs). Feeding IOCs into a SIEM provides full visibility into the network. With this information, a SIEM will correlate the logs from across the network to form a distributed set of data.
An effective CTI solution can identify various touch points as a potential hazard using the distributed data set. Instead of looking at the attack pattern as a whole, it should only need one command before automating a response and thwart an attack.
LogRhythm’s AI Engine has over 70 metadata fields that provide highly relevant data for analysis and correlation and over 900 preconfigured, out-of-the-box correlation rule sets. It can accurately define “normal” activities and automatically alarm for nefarious activities.
Make Data Actionable Out-of-the-Box
The goal of cyber threat intelligence is to draw actionable data from the thousands of log files and data streams to identify signs of nefarious behaviour. SIEMs can efficiently correlate log messages and set off alarms. Once these behaviours are detected an effective CTI product will automate your response based on the digital evidence before a breach takes place.
“It’s not just detecting a potential attack or compromise, it’s a question of what you’re going to do about it,” says Michael Orosz, director of Decision System Group, Information Sciences Institute, Viterbi School of Engineering, University of Southern California.
LogRhythm’s SmartResponse operationalizes data out-of-the-box to make it actionable. Once an alarm is set off, it enables an automated response or a semi-automated response with a sophisticated approval process.
Employ Honeypots for an Adaptive and Proactive Response
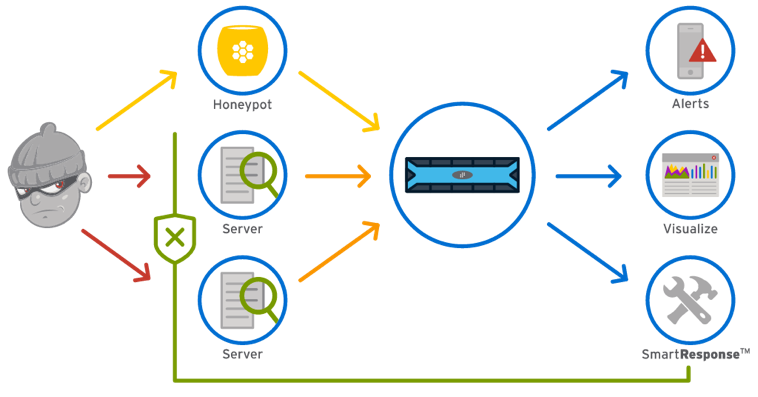
Honeypots are isolated systems such as web servers designed to look like part of the corporate network. These decoy systems are easy to exploit, to make them an attractive target for opportunist attackers.
Honeypots provide the actionable data necessary for cyber threat intelligence without compromising the network. By monitoring honeypot activity, an organization can learn about targeted threats and use this information to understand who they are being targeted by, what information their adversaries are seeking and how attack patterns will look within the network. This information enables proactive threat defence.
LogRhythm’s Honeypot Security Analytics Suite automatically tracks and analyzes an attacker’s actions to create a behaviour profile. If an observed attacker’s behaviour on the honeypot is mirrored by similar action within the environment, AI Engine automates a SmartResponse.
Cyber threat intelligence combines data left behind by attackers and innovative analytics to create the next-generation of cybersecurity intelligence.