[metaslider id=2951] … Read More
Archives for February 2017
Overcoming the Cyber Analysis Gap
From Security Magazine - Steven Chabinsky
Albert Einstein once observed, “Not everything that can be counted counts, and not everything that counts can be counted.” This admonition is particularly true when it comes to incident analysis and response.
From all of the data that can be counted, the first step is to get to the heart of what actually counts. The good news is that best-of-breed technologies are doing an increasingly good job of logging, collating, assessing and categorizing just about every computer process you can imagine, as well as many you can’t. They prevent attacks in progress and issue alerts based on pre-defined thresholds.
The bad news is that computers still can’t do everything. A gap in analysis often exists in those areas that Einstein would say count, but cannot be counted. Consider, for example, the roles that business context and business judgment play in incident response. Mature analysis programs simultaneously support tactical IT efforts (kick out the hackers while keeping the systems running), operational requirements (comply with law, including industry-specific regulations), and strategic management concerns (retain customer loyalty, establish risk appetite, and maximize the bottom line). Unfortunately, many companies limit their analysis to the tactical, potentially leaving a lot of important questions unanswered.
Overcoming the cyber analysis gap requires a focus on impact. That’s step two. Technical analysis may determine the duration of an outage or disruption to IT services, but it takes business analysis to understand how that downtime could affect clients and client relations. Technical analysis may determine the quantity and nature of customer or employee data affected, but sound legal analysis reveals a company’s resulting obligations and potential liabilities. Technical analysis may count the number of users or computers involved in a breach, but only the business units fully understand how that can impact performance targets and how best to pivot. Technical analysis may determine that key security controls were compromised, but it takes the leadership to question whether the security program was adequately resourced, staffed and executed.
The NIST Framework is a helpful tool for considering best practices for incident analysis, the goal of which is “to ensure adequate response and support recovery activities.” The underlying essentials include ensuring that notifications from detection systems are investigated, that the impact of an incident is understood, that forensics are performed when necessary, and that incidents are categorized consistent with response plans. This process should be iterative, incorporating lessons learned along the way, such as by refining alert levels and honing response plans.
To close with another Einstein saying, “The only source of knowledge is experience.” Faced with a breach, companies would do well to assemble a multidisciplinary incident response team to address their most pressing tactical, operational, and strategic objectives. After all, it often takes a company’s collective experience to know what counts, and whether or not it can be counted.
Sophos again in the Gartner Magic Quadrant as a Leader
Sophos has again been placed in the Leader Quadrant in the Gartner Magic Quadrant.
As per Gartner, Sophos strengths include the Intercept X, a behavioural ransomware protection element that allows recovery of files that were encrypted before the ransomware was detected and stopped, the Sophos Synchronized security element, communication between the firewall and endpoints and there cloud-based Sophos Central administration.
In addition the Sophos Intercept X can be installed in conjunction with any other third party antivirus software for an added layer of protection.
For more information on the Sophos product offerings - give us a call at 866-431-897, or email us.
To download the full report, visit Sophos
BitDefender Perspectives - Outsider Attacks Give Nightmares To CIOs, CEOs, CISOs
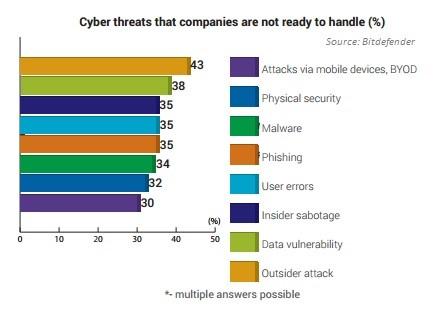
Cyberattacks via mobile devices, physical security and malware top the list of threats that US companies are not ready to handle, according to a recent Bitdefender study.
Outsider attacks give nightmares to US CIOs, according to a Bitdefender survey of 250 IT decision makers at US companies with more than 1,000 PCs. The survey notes that outsider attacks, data vulnerability and insider sabotage are the main threats companies aren’t ready to handle.
CIOs also know that cybercriminals can spend large amounts of time inside organizations without being detected; Advanced Persistent Threats (APTs) are often defined as threats designed to evade detection.
Accessing any type of data, whether stored in the private or public cloud, needs to be done via multiple authentication mechanisms, Bitdefender’s security specialists recommend. This should involve more than just usernames and passwords. For access to critical data, two-factor or biometric data offers additional control and authorization of qualified and accepted personnel. This is especially significant in organizations where access to critical and sensitive data is restricted, and only then under strict security protocols and advanced authentication mechanisms.
Insider sabotage is the third threat IT decision makers can’t yet handle
“To limit the risks of insider sabotage and user errors, companies must establish strong policies and protocols, and restrict the ways employees use equipment and infrastructure or privileges inside the company network,” recommends Bogdan Botezatu, Bitdefender’s senior e-threat specialist. “The IT department must create policies for proper usage of the equipment, and ensure they are implemented.”
In the past two years, companies witnessed a rise in security incidents and breaches, with a significant increase in documented APT type of attacks targeting top corporations or government entities (such as APT-28). This type of attack intends to exfiltrate sensitive data over a long period, or silently cripple industrial processes. In this context, concerns for security are rising to the top, with decisions taken at board level in most companies.
According to the Bitdefender survey of 250 IT decision makers at US companies with more than 1,000 PCs, IT decision makers, CISOs and CEOs are all concerned about security, not only because of the cost of a breach (unavailable resources and/or money lost), but also because their company’s reputation is at risk when customer data is lost or exposed to criminals. The more media coverage a security breach receives, the greater the complexity of the malware causing it. On top of this, migrating corporate information from traditional data centers to a cloud infrastructure has significantly increased companies’ attackable surface, bringing new threats and more worries regarding the safety of the data.
The demand for hybrid cloud, a mix of public cloud services and privately owned data centers, is estimated to be growing at a compound rate of 27% a year, outpacing overall IT market growth, according to researcher Markets and Markets. The company said it expects the hybrid cloud market to reach $85 billion in 2019, up from $25 billion in 2014. (Read the full white paper here.)
This survey was conducted in October 2016 by iSense Solutions for Bitdefender on 250 IT security purchase professionals (CIOs/CEOs/ CISOs – 26 percent, IT managers/directors – 56 percent, IT system administrators – 10 percent, IT support specialists – 5 percent, and others), from enterprises with 1,000+ PCs based in the United States of America.
Razvan, a security specialist at Bitdefender, is passionate about supporting SMEs in building communities and exchanging knowledge on entrepreneurship.